Organizational Intelligence
from Every AI Interaction
Corveil captures AI activity across your organization and turns it into actionable intelligence — daily summaries, profiles, recommendations, and more.
Book a Demo →Insights Engine
See What Your Organization Is Actually Doing
- Activity summaries — hourly, daily, and weekly digests. Know what happened without asking.
- User profiles — auto-built maps of expertise, projects, and focus areas.
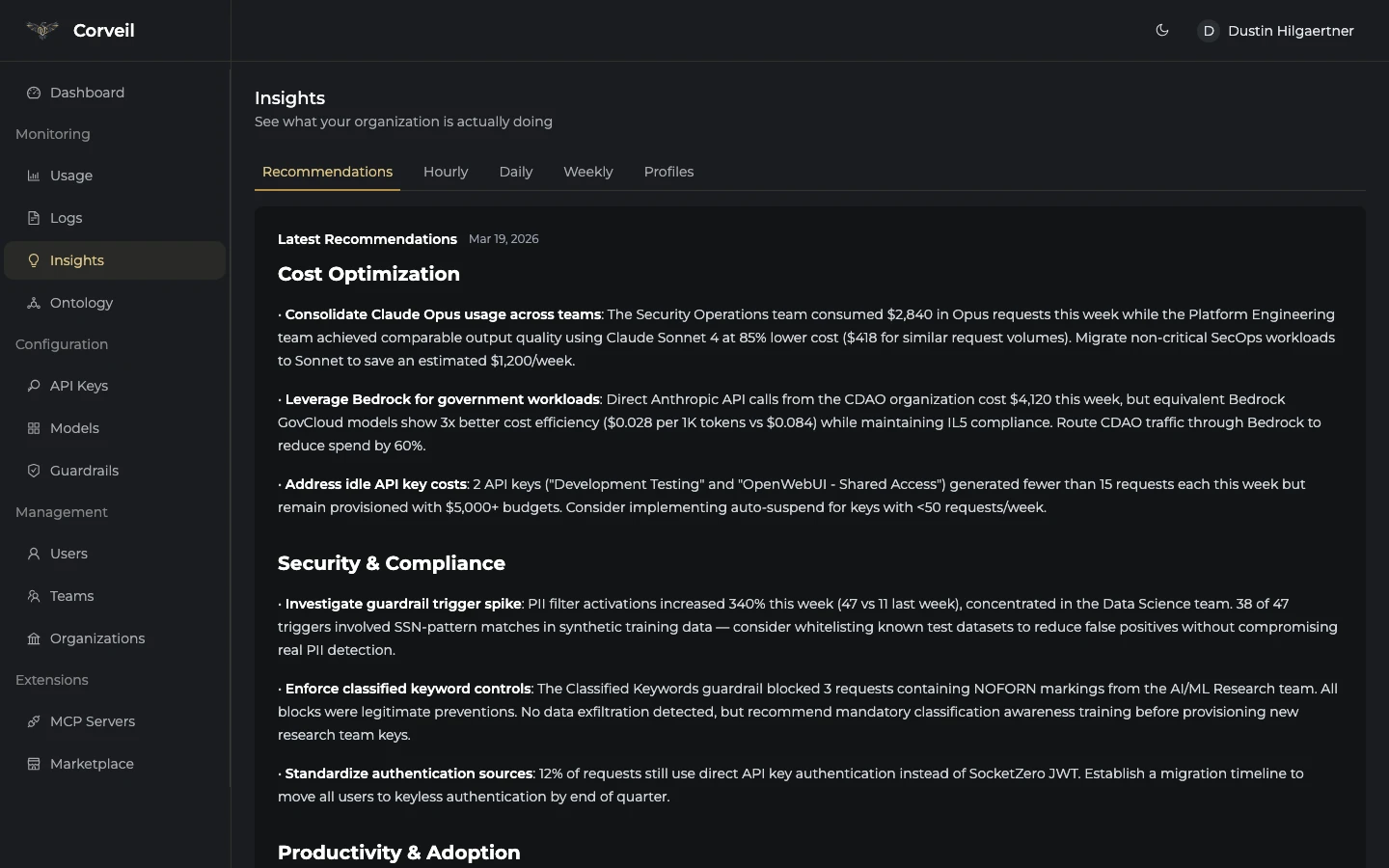
- Recommendations — actionable suggestions for cost, productivity, and security posture.
- Trend detection — surface shifts in tool adoption and workflow changes as they happen.
See It In Action
Your Organizational Command Center
Insights — Recommendations
How It Works
From AI Traffic to Organizational Intelligence
Deploy Corveil in front of your AI providers. Intelligence starts flowing immediately.
Deploy
Roll out Corveil in front of your AI providers. It sits between your tools and the models they call — invisible to daily workflows.
Capture
Every AI interaction reveals what people are working on, what problems they're solving, and where they're stuck.
Reveal
Corveil synthesizes activity into daily intelligence — summaries, profiles, knowledge graphs, and actionable recommendations.
Built For
Intelligence That Fits Your World
See What Your Organization Is Actually Doing
- Daily intelligence digests — know what happened without asking
- Execution tracking — compare daily activity against stated priorities
- Early warning signals — surface problems weeks before they reach a board deck
- Cost intelligence — AI spend visibility with optimization recommendations
- Knowledge graph — map who works on what across the entire organization
One Endpoint, Every Model
- OpenAI-compatible API — drop-in replacement, no SDK changes
- 200+ models via OpenRouter, Vertex AI, and Bedrock from one endpoint
- Streaming support — real-time token streaming across all providers
- Knowledge graph — auto-map project dependencies and team expertise
- Plugin SDK — extend Corveil with custom guardrails and automations
Zero-Trust AI Governance
- Guardrails pipeline — pre/post-call content filtering on every request
- PII filtering — detect and redact sensitive data before it reaches providers
- FIPS 140-2 compliant — security headers, encryption, AWS GovCloud ready
- Full audit trail — every request and response, indexed and searchable
- Budget caps — per-user and per-team limits that stop spend at the threshold
“We went from quarterly guesswork to daily visibility. Corveil surfaces things we didn't even know to ask about.”
“The knowledge graph alone justified the deployment. We finally know who's working on what across 12 teams.”
“Deployed on a Friday, had actionable intelligence by Monday. No workflow changes, no surveys, just signal.”
Gateway Infrastructure
The Plumbing That Powers the Intelligence
- Virtual API keys — scoped credentials per user and team. Provider keys never exposed.
- Spend tracking & budgets — real-time cost tracking with hard limits and alerts.
- Guardrails — pre/post-call content filtering. PII detection, jailbreak prevention, inline.
- Multi-provider routing — 200+ models through OpenRouter, Vertex AI, and Bedrock.
Claude Code Cursor aichat Codex OpenClaw
\ | | | /
\ | | | /
┌────────────────────────────────────────┐
│ C O R V E I L │
│ │
│ Auth → Guardrails → Route → Log │
│ Insights Engine │
└────────────────────────────────────────┘
/ | | \
/ | | \
OpenRouter Vertex AI Bedrock Azure
200+ models Gemini GovCloud OpenAIGet Started
Deploy Corveil in Minutes
Choose the deployment method that fits your infrastructure.
helm upgrade --install corveil oci://ghcr.io/radiusmethod/citadel-helm/citadel-chart \
--set citadel.environment=development \
--set citadel.devLoginEnabled=true \
--set providers.openrouter.apiKey="sk-or-xxx"Requires Helm 3.x and a running Kubernetes cluster.
git clone https://github.com/radiusmethod/corveil-docker-compose.git cd corveil-docker-compose docker compose up -d
Starts Corveil, PostgreSQL, and Redis with sensible defaults.
# Install the latest binary (downloads, verifies SHA-256 checksum, installs) curl -sSL https://corveil.com/install.sh | sh # Start in single-user mode corveil --dev --openrouter-api-key sk-or-...
Single static binary for Linux and macOS. The installer automatically verifies the download against published SHA-256 checksums before installing. No containers or database setup required. Dashboard opens at localhost:8000. Manual downloads & checksums →
# Install the Corveil skill from ClawHub openclaw skill install corveil # Run the skill to start Corveil and configure routing openclaw skill run corveil
Installs and runs Corveil via OpenClaw. The skill handles binary installation, startup, API key creation, and provider routing configuration automatically. OpenClaw setup guide →
Connect Your AI Tools
Works with the Tools You Already Use
Point your favorite AI tool at Corveil. No SDK changes required.
aichat
Terminal AI chat. YAML config, OpenAI-compatible.
DirectClaude Code
Anthropic's CLI agent. Direct and Passthrough modes.
Direct + PassthroughOpenClaw
AI gateway client with custom header support.
PassthroughCursor IDE
AI code editor. GUI-based endpoint config.
DirectOpenCode
Open-source terminal coding assistant.
DirectCodex CLI
OpenAI's coding agent with custom TLS.
DirectFAQ
Frequently Asked Questions
What is Corveil?
Corveil is an organizational intelligence platform that acts as a zero-trust AI gateway. It routes LLM requests through a single secure endpoint while capturing knowledge about how your organization uses AI — building a knowledge graph of people, projects, technologies, and decisions.
Is Corveil free?
Yes. Corveil is free to download and run. The binary ships as a single static executable. Bring up the included Postgres + pgvector docker-compose alongside it and you have a fully functional gateway with an admin dashboard and all features enabled.
Does Corveil work with Claude Code?
Yes. Claude Code connects to Corveil by setting ANTHROPIC_BASE_URL to your Corveil instance. Corveil supports both Direct mode (Corveil provides the API key) and Passthrough mode (Claude Code Max users route through Corveil for logging and guardrails while using their own subscription).
What is organizational intelligence?
Organizational intelligence is the understanding of who knows what, who works on what, and how your organization actually operates. Corveil builds this automatically by analyzing AI activity — extracting entities like people, projects, and technologies from conversations and mapping the relationships between them into a searchable knowledge graph.
What LLM providers does Corveil support?
Corveil supports Anthropic (Claude), OpenRouter (200+ models including GPT-4, Llama, Mistral), Google Vertex AI (Gemini), and AWS Bedrock (including GovCloud). All providers are accessed through a single OpenAI-compatible API endpoint.
Does Corveil support self-hosted deployments?
Yes. Corveil is designed for self-hosted deployment. It ships as a single Go binary that runs anywhere — bare metal, Docker, Kubernetes (via Helm chart), or cloud platforms like AWS GovCloud. Your data never leaves your infrastructure.
How is Corveil different from other AI gateways?
Most AI gateways are proxies — they route traffic and log requests. Corveil does that too, but it also builds organizational intelligence: a knowledge graph that maps relationships across people, projects, and technologies, plus an insights engine that produces daily and weekly activity summaries. It is the difference between a proxy and a platform.












